The role of a Microsoft CSP is not limited to just selling services and subscriptions to customers. A Microsoft CSP is supposed to provide end-to-end cloud solutions to the customers along with technical support and account management. To achieve this, a Microsoft CSP needs to have access and permission to manage the customer’s account. Delegated Administration Privileges (DAP) enable Microsoft CSPs to manage the subscriptions of a customer on their behalf. DAP is the original model through which a customer can grant administrative permissions to Microsoft CSP. Under the DAP model, once a customer accepts the invitation to establish a reseller relationship with a CSP, the CSP can perform a large number of tasks for the customers. Under the DAP model, partners are allowed broad privileges to manage their customers’ accounts. Once the customer accepted a DAP agreement, the partner was able to assign the global admin role to their employees. Thus, giving the partner’s employees access to the sensitive data of the customer and its employees. They can also make the following changes to the account:
- Adding users and managing accounts
- Resetting user passwords
- Making purchases
- Managing licenses and subscriptions
- Adding and managing web domains associated with the customer’s organization
Once the DAP is activated, the Microsoft CSP can add as many global admins as possible to manage the customer account. Thus, creating security and compliance risks. All the customers might not be comfortable with the level of access the existing DAP model allows to the partners. They might have reservations about the security measures in place to safeguard their data. As per a report by Gartner on top trends in cyber security, 2022“ by 2025, 45% of organizations worldwide will have experienced attacks on their software supply chains, a three-fold increase from 2021.”
To address the security concerns and to implement a zero-trust security model, Microsoft is ending DAP and replacing it with a new model, Granular delegated Admin Privileges (GDAP). Transitioning from DAP to GDAP is mandatory for all Direct Bill Partners, Indirect Providers, and Indirect Resellers in the CSP program.
Microsoft plans to start the transition of all active as well as inactive DAP relationships to GDAP relationships from May 22, 2023. GDAP reduces security concerns by providing the CSPs with the least-privileged access. Under this model, the Microsoft CSPs will have specific and time-bound access to the customer’s account and sensitive data.
Microsoft has described GDAP as “GDAP is a security feature that provides partners with least-privileged access following the Zero Trust cybersecurity protocol. It lets partners configure granular and time-bound access to their customers’ workloads in production and sandbox environments. This least-privileged access needs to be explicitly granted to partners by their customers.
Thus with the introduction of GDAP, Microsoft aims to tighten up controls and improve the security and compliance posture of the Microsoft CSP program.
Benefits of GDAP over DAP
GDAP has numerous advantages over DAP for both Microsoft CSPs as well as its customers. GDAP has several security features that were not available with DAP making it beneficial for partners to migrate. Some of the benefits of GDAP are as follows:
Custom Access
Under the DAP model, once the reseller relationship is established, the global admin role and helpdesk admin roles are provided by default. This gives Microsoft CSP access to a broad level of administrative functions of the customer’s account. As the CSPs are given global admin permissions and they can assign global admin roles to their employees. These roles were the same for all the customers and there was no option to customize the access under the DAP model which gave complete access to the customer account and data to the CSPs. This can create a serious security risk if the security posture at the partner’s end is compromised. Customers can choose from the various partner roles that are available with Azure AD. Thus, allowing Microsoft CSP and its employees limited access to the sensitive data of the customer.
More control
In a DAP relationship as the Microsoft CSP gets global admin rights, they could assign as many of their employees as global admins. Customers had no control over the number of global admins added by the partner as they were capable of only accepting or denying partner access to their account. Many organizations are looking to implement zero-trust to reduce risks. According to Gartner, “by 2026, 10% of large enterprises will have a mature and measurable zero-trust program in place, up from less than 1% today.” GDAP adheres to the zero-trust principle of least privileged access. This can limit potential risks between Microsoft CSPs and their customers.
GDAP allows the creation of nested security groups, which gives more control to customers to stratify permissions. Diverse groups can be granted distinct permissions based on business requirements. This allows customers to have more control over who and how much of their data can be accessed.
Defined relationship duration
The DAP relationships were indefinite with no option of expiration after a set duration or after a period of inactivity. This allowed the partners to have access to customer data and permission to take tenant-wide actions until the relationship was removed. To keep themselves secure, customers had to regularly review their DAP relationships so that they could remove the ones that were no longer needed or were inactive. This increases the customer’s workload and can lead to unwanted access if any DAP relationship is overlooked.
GDAP allows the setting of custom relationship duration between the Microsoft CSP and the customer. This relationship can be set up for a maximum period of 730 days i.e. 2 years. Post the defined relationship duration, the GDAP relationships automatically expire and the partner is no longer able to access the customer’s account. This creates a more secure environment.
Better compliance
DAP did not provide any activity logs for the customer to see when the partner is accessing or making any changes to the customer account. As a result, it was difficult to identify unauthorized changes and take corrective action on time.
GDAP provides granular activity logs by which both the partners as well as the customers can track who performed specific tasks and when. The improved audibility combined with access control helps stay compliant with various regulatory requirements related to data privacy and security Various regulations and standards such as HIPPA, GDPR, FISMA, ISO, SOC, etc require the application of least-privilege access policies.
Timelines for DAP to GDAP transition
In November 2021, Microsoft announced that it will soon introduce a fine-grained delegated access model to reduce the security risk for customers. This announcement was covered in one of our earlier blogs.
Microsoft announced the new GDAP milestone dates in February 2023. According to this announcement, from May 22, 2023, the following will take place:
- The transition of active and inactive DAP relationships to GDAP with limited Azure Active Directory (AD) roles will start.
- Once the relationship has been transferred from DAP to GDAP, Microsoft will remove the relevant DAP relationship after a period of 30 days of the transition.
- Due to the fiscal year closure, Microsoft will pause the transition in the month of June 2023.
You can read the announcement here.
As per Microsoft’s announcement on 15 March 2023, it will soon finalize the GDAP milestone dates for the following:
- Bulk migration tool- The date when the bulk migration tool for the removal of DAP relationships and creating GDAP relationships will be retired.
- Customer creation- The date when Microsoft will stop granting DAP for new customer creation and instead GDAP with default roles will be granted on new customer creation.
How to plan the transition from DAP to GDAP as a Microsoft CSP?
As the date when Microsoft will start the transition from DAP to GDAP comes closer, as a Microsoft CSP, you need to plan for the migration so that the customer workloads are unaffected and there is no impact on business continuity. If GDAP is not enabled on customer tenants, you will not be able to earn Partner Earned Credits (PECs) and incentives and will be unable to provide any support to your customers. The following steps can help you transition smoothly from DAP to GDAP.
Review current DAP connections
The first step of the transition is to review all the existing DAP relationships with your customers. A DAP monitoring report can be accessed from the Microsoft Partner Center for reviewing the existing DAP connections. With this report, you will be able to differentiate between active and inactive DAP connections. This process will help you identify which DAP relationships have to be removed and which DAP relationships have to be transitioned to GDAP. Once you have identified the inactive DAP relationships, delete them after notifying your customers. Once the relationship is removed, your employees will lose all access to the customer’s account. This will ensure that only the active DAP relationships get migrated to GDAP.
Plan and decide on roles
Once you established a DAP relationship with a customer, you were assigned the global admin role by default. You could also assign global admin roles to your employees giving them unrestricted access to the customer’s workloads and data. With GDAP, access to the customer’s account will be customized and restricted to specific roles that your employees have to perform on behalf of the customer.
So before you begin the transition from DAP and GDAP, you need to have a fair understanding of the various tasks and their frequency that you and your employees perform for the customers. This will help you understand the different roles your team needs access to. These tasks can include adding or changing users, license management, making purchases, resetting user passwords, managing domain names, creating service requests, etc.
Once you have the list of activities in place, the next step is to determine the minimum roles you need to support your customers. You can choose between different least privileged roles that are required to perform each task under the GDAP capability. These include managing support, users, licenses, and groups. There are various roles that are available such as directory readers, directory writers, global readers, license administrators, service support administrators, user administrators, privileged role administrators, helpdesk administrators, privileged authentication administrators, groups administrators, etc. Support articles prepared by Microsoft can help you in deciding on the roles.
Establish GDAP relationship
Once the tasks and the corresponding roles have been identified, you can begin the process of transitioning from DAP to GDAP. For this, you will have to obtain granular admin permission from the customer. To establish a GDAP relationship
- Sign into the partner center and select customers.
- Select the specific customer you wish to request a GDAP relationship.
- Now select Admin relationships, followed by Request admin relationship.
- On the next page, you fill out a form to create an admin relationship request. Here you need to provide the Admin relationship name as well as the duration. The admin relationship name will be visible to the customers and should be unique. The duration of the relationship could be set up to 730 days.
- The next information that must be added to the relationship request is the Azure AD roles. You can select the roles which you need to assign to your team.
- Once you have selected the Azure AD roles, they will appear in the Requested Azure AD roles section.
- If you need to add or delete roles, you can repeat the steps above.
- After you have finalized the admin relationship name, duration, and Azure AD roles, click on Finalize request.
- By doing so you will be able to see a permission request e-mail message for your customer. You can review and edit the content of the message. Do not make any changes to the link under Click to review and accept as this is a personalized URL for your customer.
- Send the e-mail and once the customer accepts the request GDAP will be established.
You can also use the GDAP bulk migration tool prepared by Microsoft to transition to GDAP. Microsoft will soon be announcing the date when the bulk migration tool will be retired.
Disable existing DAP relationships
Once you have completed the transition to GDAP and are sure that you can perform the necessary activities on behalf of your customer, you can start removing the DAP relationships. This is to be done to improve customer security.
You can disable the DAP relationships by accessing the Security Center on the Partner Center. Under the Account Settings, you can see Administrative Relationships, here you can select one or multiple customers and then click on disable DAP. This will remove the selected DAP relationships. There will be no impact on Partner Earned Credits (PEC) if you disable a DAP relationship.
Train and monitor your team
As a Microsoft CSP, you need to train your employees so that they can access the Azure AD portal and perform their tasks efficiently. You can begin by giving your employees an overview of GDAP and how their level of access will change with the transition from DAP to GDAP. The employees should understand the roles they have been assigned. They should know what tasks they are authorized to perform and what tasks they cannot perform. The employees should be trained on security best practices so that they are capable of handling sensitive customer data.
As GDAP provides activity logs for both partners as well as customers, you can regularly review them to ensure that your employees are only accessing data that is relevant to the tasks they have to carry out.
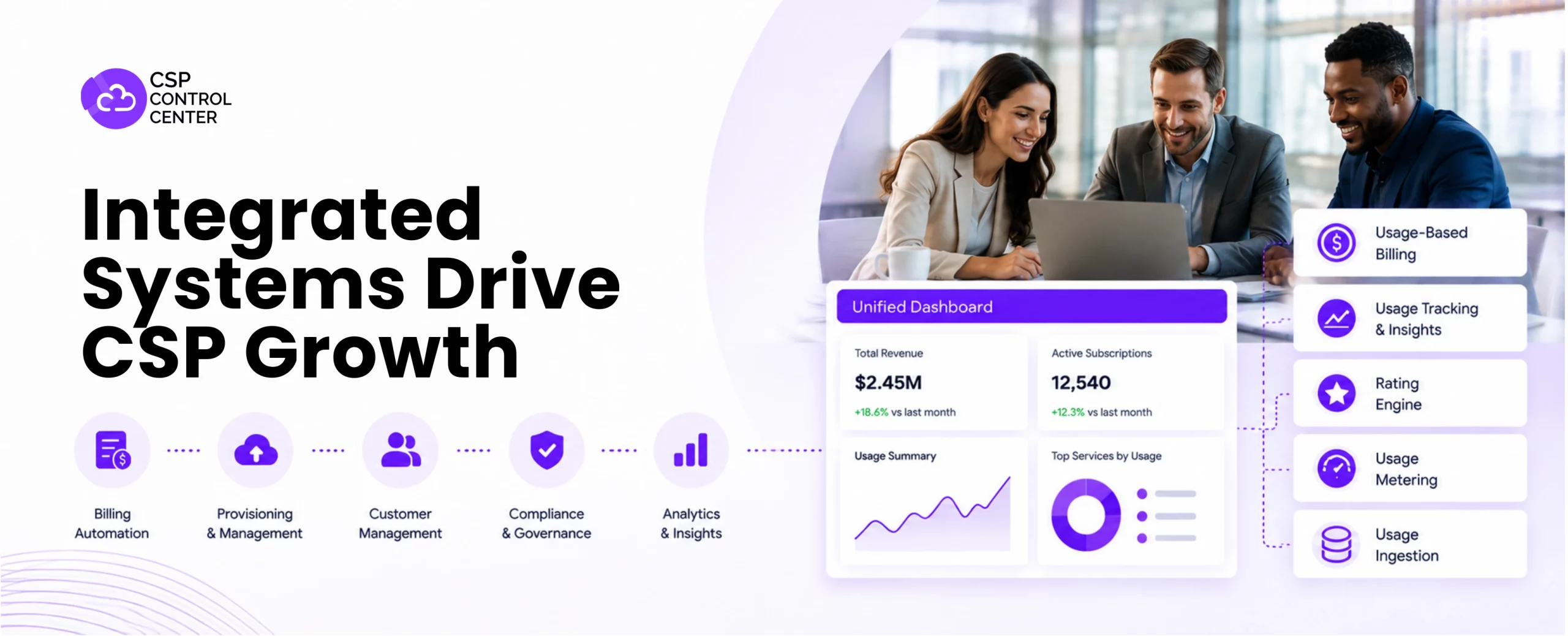
CSP control center supports GDAP security
Are you worried about managing customer subscriptions and billing post transitioning to GDAP? Partner with C3 and keep your worries aside because C3 offers you the ultimate CSP billing automation solution that supports GDAP security. There will be no change in the way you handle the billing, purchase, subscription management for your customers after the shift from DAP to GDAP. C3 can help streamline your Microsoft CSP business allowing you to focus on the transition from DAP to GDAP.
- Leverage automated invoicing and billing to save time and resources.
- Offer self-service capabilities to your customers to reduce the dependence on your customer support team.
- Use smart integrations to run your Microsoft CSP business seamlessly.
- Safeguard your customers safe from hackers and data breaches by using secure payment gateways provided by C3.
Get in touch to know more about the benefits of C3 for your Microsoft CSP business.

 CSP Control Center
CSP Control Center
 CloudEvents
CloudEvents